


*This is the third part of our three-part series on C-Suite executives and how their roles are influenced by the growing risks in cybersecurity.
Find them here:
Part 1: “5 Reasons Why Every CEO Must Be Cyber Secure”
Part 2: “From Techie To Business Leader: The CISO’s New Threat”
Gartner research predicts that over the next 3 years, manual distribution of malicious content via social media will be the highest growing trend.
But is malicious content the only concern for CMOs in the realm of cyber? Sadly, there are more concerns than malicious content alone.
Hackers live to infuse broken or malicious links into your social media accounts. When they succeed, hackers can leverage thousands of customer details and credit card accounts at the click of a button.
But cyber criminals aren’t the only risk to your brand. They’re accompanied by ‘ordinary’ criminals, who can exploit your brand to get other monetary gains; selling fake, compromised products and claiming they are genuine, luxury goods.
Just ask the designers. Within 24 months until March 2015, UK handbag brand, Mulberry, took down 3,321 websites selling fake merchandise, under their (fake) high street label.
The damage is endless. Hackers can create fake accounts that masquerade as your brand or as your employees; selling bogus product, distributing malware, broadcasting false information, stealing account credentials, or simply humiliating your brand in communities you have no control over.
Have you heard of ‘HAMMERTOSS’? Hopefully, you won’t ever need to know about it, but either way, you should know about it on a pre-emptive level.
HAMMERTOSS is a malware backdoor that exploits Twitter, GitHub, and cloud storage tools in order to send commands and extract data from the networks it compromises.
HAMMERTOSS mimics normal user behavior, although what it’s actually doing is spying on its victims’ computer systems.
This backdoor was created by APT 29. APT is the name of an attack-type, Advanced Persistent Threat. It means that with HAMMERTOSS, too, except it’s also the name of the hacking group, APT29, who FireEye believe are a hacking group sponsored by the Russian government.
HAMMERTOSS uses an algorithm that retrieves images from regular tweets via GitHub, and through these images and the code their files provide, HAMMERTOSS can offload sensitive info from the computer that stores the image — onto a hacker-run cloud server (or C&C servers — in cyber terms).
No CMO wants their company’s tweets, nor anybody reading, retweeting, or engaging with these tweets — to be targeted by a malware like HAMMERTOSS.
In 2014, the Anti-Counterfeiting Group (ACG) identified the availability of over 30,000 individual images of counterfeit goods in just one day on Facebook.
30,000 sales of counterfeit products? Regardless of how many of these ‘goods’ ended up being sold from this number of images, this stat is troublesome in its own right.
It happened to Gucci with Alibaba’s sellers. And it wasn’t pretty;
Alibaba’s TaoBao shopping service, built a campaign, in which they (falsely) claimed to be selling wholesale quantities of Gucci bags.
The seller advertised a branded handbag for $2-$5 (£1.30-£3.20) per unit – with the price determined by the size of the order, which had to be a minimum of 2,000 bags. This is a ‘sweet deal’ for any retailer, because one of these Gucci bag regularly costs $795 each.
Disheartened Shoppers = Distressed CMOs
This story is troubling for many people; for ripped off buyers, for the companies selling the original products, but also, for these companies’ marketing pros.
You want complete control over your products, who’s getting them, and how, but most of all, you always want to know about it, even if you’re not gonna like it.
If anybody on Facebook is selling (or talking about selling) ripoffs of your product, you need to know about it first.
You need complete visibility into who is talking about your brand, and most of all, into what they’re saying.
Nobody likes brand abuse crises, especially not in their most detrimental form. That’s what brand abuse crises on Facebook are: the worst possible type of brand abuse, because the number of people who can see it is unquantifiable.
The ability of Facebook campaigns to spread like wildfire is no laughing matter. Facebook uses the EdgeRank algorithm: fans that like, comment, or share your brand/company’s post, are, thanks to the algorithm, almost certain to see all engagements that follow it.
In terms of brand shaming, this means that once a ‘negative sentiment’ is posted to your page, not only can all your fans see it, whoever engages in its discussion or shares it onward, will see all the dialogue that spirals out of the original post.
If one comment wasn’t bad enough, imagine the impact of every comment and share that follows.
Take the unfortunate example of Applebee’s, a restaurant chain in the US.
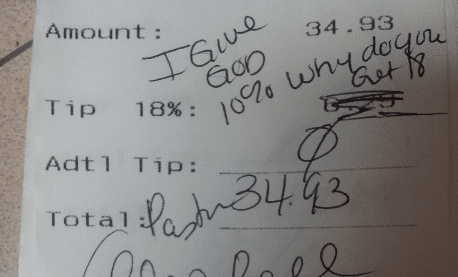
A dissatisfied customer left his waitress a note on his bill, in response to the mandatory 18% tip that he was charged for after his meal. Apparently, this customer wasn’t enthused about forking over an 18% tip, especially since, “he only gives God 10%.”
Tip or no tip aside, the waitress took a photo of this receipt and posted it to Reddit, to then eventually be fired for “violating customer privacy”. Eventually, the image made its way around social media, and Applebee responded with a short, defensive post on their Facebook page. Attempting to tame the mayhem that unraveled, Applebee’s resolution efforts only backfired;
Their post earned 10,000 comments in one day, most of which were negative. By the end of the following day, the post had acquired 19,000 comments. Applebee’s then responded by deleting the posts, but that by no means rectified the already-done damaged.
Facebook’s EdgeRank algorithm succeeded, because the amount of comments on Applebee’s first post doubled in size over 24 hours, and that’s only representing the users who commented on it. The number of users who saw the post but didn’t react, probably has too many zeroes to fit on one page.
Applebee’s Facebook fiasco is a CMO’s nightmare. Even one negative comment on your company’s Facebook page is a massive blow to your customer success and your brand sentiment.
This danger may not be cyber-based, but it’s harmful nonetheless, and Applebee’s would have been a lot better off had they known that their ex-employee was starting banter on Reddit.
Social Media that’s Monitored by Intelligence
Negative brand sentiment and malware each pose different, yet dire threats to companies’ brand identities, and the possibilities are painful to imagine.
Our automated intelligence provided by Argos, along with our CyberOPS team of (human) analysts, monitors social media in real time.
Our cyber intelligence platform spots brand chatter and attempts at malicious activity in real time. In practice, this means we’ll know about any attempt before it materializes, and in essence, so will you.
Fill in your business email to start

